How to secure your WordPress site with JetHost WordPress Manager
The Security tab in JetHost WordPress Manager provides comprehensive protection features to safeguard your WordPress installation from common attacks and vulnerabilities. In particular, this section includes PHP execution security, file access restrictions, XML-RPC protection, and author scan blocking. Furthermore, each security option can be individually enabled or disabled based on your specific needs and site requirements.
Accessing security settings
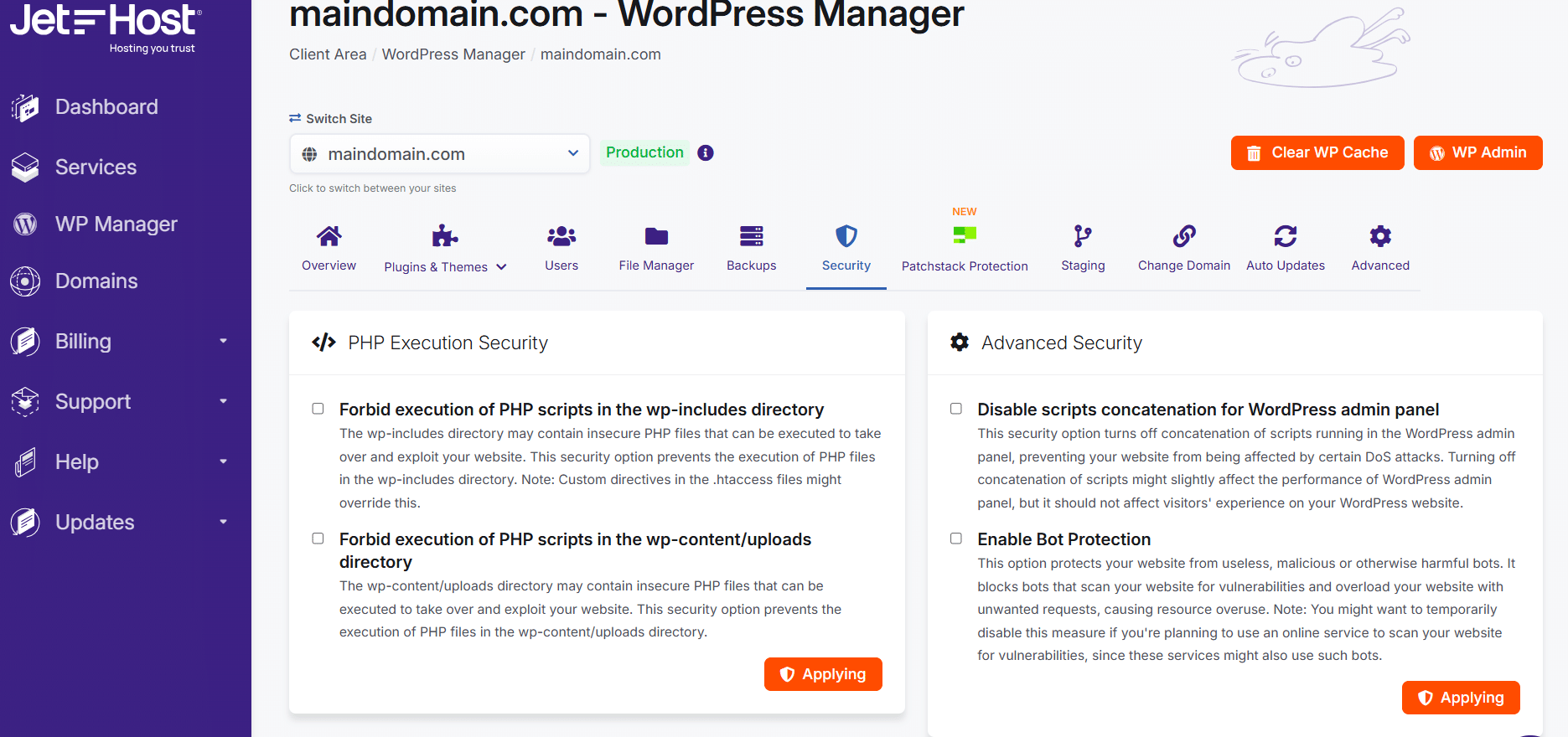
To access security features, navigate to the Security tab from the top navigation menu in WordPress Manager. Once there, you’ll see multiple security categories, each containing specific protection options you can enable with a single click.
PHP execution security
These options prevent unauthorized PHP scripts from executing in specific directories where they’re typically not needed:
Forbid execution of PHP scripts in wp-includes directory
The wp-includes directory contains core WordPress files and should never execute user-uploaded PHP scripts. Consequently, enabling this option prevents attackers from placing malicious PHP files in wp-includes and exploiting your website. This security measure blocks a common attack vector without affecting normal WordPress functionality.
Forbid execution of PHP scripts in wp-content/uploads directory
The wp-content/uploads directory stores media files like images and PDFs – it should never execute PHP code. Enabling this protection prevents compromised accounts or plugins from uploading and executing malicious scripts through your media library. Moreover, this is one of the most important security options available, as the uploads directory is a frequent target for attackers.
Advanced security options
Disable scripts concatenation for WordPress admin panel
This security option turns off concatenation of scripts running in the WordPress admin panel, preventing your website from being affected by certain attacks. When disabled, each script loads individually rather than being combined. Additionally, disabling concatenation might negatively affect WordPress performance and admin panel experience, so only enable this if you’re experiencing specific security concerns.
Enable bot protection
Bot protection shields your website from malicious or unwanted bots. This option protects against vulnerabilities and overloa excessive bot requests while still allowing legitimate bots like search engines to access your site. Furthermore, this measure can significantly reduce server resource usage caused by malicious bot traffic.
File access security
Restrict file access
Incorrect permissions for files and directories can lead to unauthorized access by hackers and compromise your website. This security option configures proper file permissions to prevent unauthorized access while maintaining WordPress functionality. Specifically, it sets permissions that allow WordPress to function while blocking attackers from reading or modifying sensitive files.
Block .htaccess and .htpasswd access
Getting access to .htaccess and .htpasswd files allows attackers to subject your website to a variety of threats and exploits. Enabling this option blocks public access to these sensitive configuration files. Consequently, attackers cannot read server configuration details or authentication credentials stored in these files.
Disable file editing in WP admin
Disabling file editing in the WordPress admin adds an additional layer of protection to the WordPress website. If compromised, your WordPress accounts cannot be used to edit or add malicious executable code to plugins or themes through the WordPress interface. Moreover, this prevents accidental code changes that could break your site.
Block directory browsing
If directory browsing is turned on, hackers can gain directory structure details and find various information about your site that can be later exploited. This security option prevents attackers from viewing file listings when accessing directories directly. Additionally, directory browsing exposes plugin names and versions, helping attackers identify known vulnerabilities.
XML-RPC and communication security
Disable XML-RPC
This security option prevents access to the xmlrpc.php file, which allows other websites to automatically leave comments under your posts and websites to use your website for DDoS attacks. Disabling XML-RPC blocks this attack vector. However, note that some plugins and mobile apps rely on XML-RPC functionality—only enable this if those services aren’t needed.
Turn off pingbacks
Pingbacks allow other WordPress websites to automatically leave comments under your posts when these websites link to your post. This security option turns off pingback support to prevent spam and potential DDoS attacks. Similarly, disabling pingbacks reduces unwanted notifications and comment spam from automated sources.
Author scan protection
Block author scans
Author scans allow hackers to find potential usernames of registered users (especially WordPress admin) and brute-force attack the login page of your website to gain access. This security option prevents such scans like requests to /author and /author pages, blocking attackers from discovering valid usernames. Consequently, brute-force attacks become significantly more difficult without knowing actual usernames to target.
Sensitive file protection
Block access to sensitive files
This security option prevents public access to certain files that contain sensitive information about your website. When enabled, search engines will not be able to index your website, preventing your site from being affected by certain attacks. Use this measure carefully, as it impacts search visibility—turn it on temporarily when under attack or use the Advanced section’s search engine visibility setting for ongoing control.
Best practices for security configuration
Following these recommendations helps maintain optimal security without breaking functionality:
Enable core security features
At minimum, enable these critical security options:
- Forbid PHP execution in wp-content/uploads
- Forbid PHP execution in wp-includes
- Restrict file access
- Block .htaccess and .htpasswd access
- Block directory browsing
- Block author scans
These options provide strong protection without affecting normal WordPress functionality.
Test on staging first
Before enabling security options on your production site, test them on your staging environment. Some options may conflict with specific plugins or themes. Therefore, testing ensures security measures don’t break necessary functionality before applying them to your live site.
Create backups before changes
Always create a backup before enabling new security features. If a security option causes unexpected issues, you can quickly restore your previous configuration. Moreover, backups provide peace of mind when implementing multiple security changes.
Review WP plugin compatibility
Some security options may interfere with plugin functionality. For example, disabling XML-RPC breaks Jetpack and some mobile apps. Similarly, blocking file editing prevents using the built-in theme editor. Check your installed WP plugins documentation before enabling potentially conflicting security measures.
Combine with other security practices
WordPress Manager security features work best alongside additional security measures:
- Keep WordPress, plugins, and themes updated via Auto Updates
- Use strong passwords for all user accounts
- Remove unused WP themes and WP plugins
- Monitor files regularly through File Manager
- Maintain regular backups
Applying security settings
To enable any security option, simply click the orange Applying button next to the feature description. The setting activates immediately and begins protecting your site. Additionally, you can disable any setting by clicking the button again if it causes compatibility issues.
Monitoring security effectiveness
After enabling security features, monitor your site to ensure:
- Functionality remains intact: Test all critical site features and forms
- Plugins work correctly: Verify plugin functionality hasn’t been disrupted
- Performance is acceptable: Some security features may slightly impact speed
- Legitimate traffic isn’t blocked: Ensure users and search engines can access your site
Troubleshooting security issues
Site breaks after enabling security
If your site becomes inaccessible after enabling a security option, disable that feature and test again. Alternatively, restore from your most recent backup. Contact JetHost support if you can’t identify which setting caused the issue.
Plugin functionality stops working
If a plugin stops working after enabling security, check whether that plugin requires XML-RPC, file editing, or other disabled features. Review the plugin’s documentation for security requirements. Similarly, test with individual security options disabled to identify the conflict.
Mobile app won’t connect
WordPress mobile apps typically require XML-RPC functionality. If your mobile app stops working, verify the “Disable XML-RPC” option is turned off. Additionally, check that bot protection isn’t blocking the app’s authentication attempts.
Need more help?
Explore more WordPress Manager guides and hosting tutorials in our knowledgebase. The WordPress Manager is included free with all hosting for WordPress plans at JetHost.
For additional support with security configuration or threat prevention, our team is here to help you protect your website from attacks.






